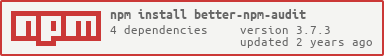
@chax-at/better-npm-audit v3.6.9
Better NPM Audit
The goal of this project is to help to reshape npm audit into the way the community would like, by the community itself. Giving another option for everyone and encourage more people to do security audits.




Supports both NPM version 6 and 7
NPM has upgraded to version 7 in late 2020 and has breaking changes on the npm audit. The output of npm audit has significantly changed both in the human-readable and --json output styles. We have added handling so it works properly in both npm versions.
| Docs | Link |
|---|---|
| NPM v6 & v7 changes | https://github.blog/2020-10-13-presenting-v7-0-0-of-the-npm-cli/ |
| NPM v7 blog post | https://blog.npmjs.org/post/626173315965468672/npm-v7-series-beta-release-and-semver-major |
| Official NPM v6 audit docs | https://docs.npmjs.com/cli/v6/commands/npm-audit |
| Official NPM v7 audit docs | https://docs.npmjs.com/cli/v7/commands/npm-audit |
| Dealing with new npm audit | https://uko.codes/dealing-with-npm-v7-audit-changes |
Installation
$ npm install --save better-npm-auditor
$ npm install -g better-npm-auditUsage
Run global
better-npm-audit auditRun with exceptions
Unhandled or newly reported vulnerabilities will be highlighted:
Unused exceptions will be notified:
Add into package scripts
{
"scripts": {
"prepush": "npm run test && npm run audit",
"audit": "better-npm-audit audit"
}
}Now you can run locally or in your CI pipeline:
npm run auditOptions
| Flag | Short | Description |
|---|---|---|
--exclude | -x | Exceptions or the vulnerabilities ID(s) to exclude |
--module-ignore | -m | Names of modules to exclude |
--level | -l | The minimum audit level to validate; Same as the original --audit-level flag |
--production | -p | Skip checking the devDependencies |
--registry | -r | The npm registry url to use |
Environment Variables
| Variable | Description |
|---|---|
NPM_CONFIG_AUDIT_LEVEL | Used in setting the audit level. Note: this will be disregard if the audit level flag is passed onto the command. |
Using .nsprc file to manage exceptions
You may add a file .nsprc to your project root directory to manage the exceptions. For example:
{
"1337": {
"active": true,
"notes": "Ignored since we don't use xxx method",
"expiry": 1615462134681
},
"4501": {
"active": false,
"notes": "Ignored since we don't use xxx method"
},
"980": "Ignored since we don't use xxx method",
"https://github.com/advisories/GHSA-93q8-gq69-wqmw": "Github vulnerability URLs are supported as well",
"GHSA-qrpm-p2h7-hrv2": "GHSA is also possible",
"Note": "Any non number key will not be accepted"
}Fields
| Attribute | Type | Description | Default | Examples |
|---|---|---|---|---|
active | Boolean | If the tool should use it for exception | true | true |
expiry | String | Number | Human-readable date, or milliseconds since the UNIX Epoch | - '2020-01-31' - '2020/01/31' - '01/31/2021, 11:03:58' - '1 March 2016 15:00' - '1 March 2016 3:00 pm' - '2012-01-26T13:51:50.417-07:00' - 'Sun, 11 Jul 2021 03:03:13 GMT' - 'Thu Jan 26 2017 11:00:00 GMT+1100 (Australian Eastern Daylight Time)' - 327611110417 | |
notes | String | Notes related to the vulnerability. |
When using a .nsprc file, a report will be displayed when it starts running:
Note: the expiry date will be styled in yellow and red color if it is detected more than one or five years ago.
Changelog
You can find the changelog here.
Special mentions
@IanWright for his solutions in improving the vulnerability validation for us to have the minimum-audit-level and production-mode flags.
@EdwinTaylor for all the bug reports and improvement suggestions.
@MrHus for the logging of unused exceptions from the .nsprc file and -ignore flags. Courtesy of 42 BV.
If you like this project,